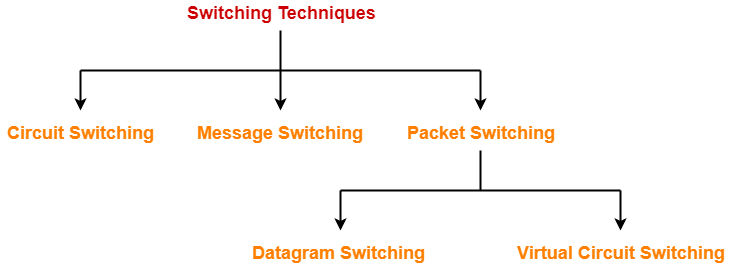
Switching in Computer Networks-
| The process of moving the data packets towards their destination by forwarding them from one port to the other port is called as switching. |
Switching Techniques-
Various switching techniques are-
In this article, we will discuss about Packet Switching.
Packet Switching-
In packet switching,
- The entire message to be sent is divided into multiple smaller size packets.
- This process of dividing a single message into smaller size packets is called as packetization.
- These smaller packets are sent after the other.
- It gives the advantage of pipelining and reduces the total time taken to transmit the message.
Optimal Packet Size-
If the packet size is not chosen wisely, then-
- It may result in adverse effects.
- It might increase the time taken to transmit the message.
So, it is very important to choose the packet size wisely.
Example-
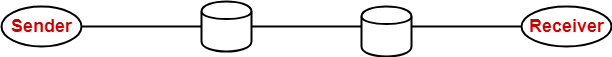
Consider-
- There is a network having bandwidth of 1 MBps.
- A message of size 1000 bytes has to be sent.
- Packet switching technique is used.
- Each packet contains a header of 100 bytes.
Out of the following, in how many packets the message must be divided so that total time taken is minimum-
- 1 packet
- 5 packets
- 10 packets
- 20 packets
NOTE
|
Let us analyze each case one by one.
Case-01: Sending Message in 1 Packet-
In this case, the entire message is sent in a single packet.
Size Of Packet-
Packet size
= 1000 bytes of data + 100 bytes of header
= 1100 bytes
Transmission Delay-
Transmission delay
= Packet size / Bandwidth
= 1100 bytes / 1 MBps
= 1100 x 10-6 sec
= 1100 μsec
= 1.1 msec
Total Time Taken-
Total time taken to send the complete message from sender to receiver
= 3 x Transmission delay
= 3 x 1.1 msec
= 3.3 msec
Case-02: Sending Message in 5 Packets-
In this case,
- The entire message is divided into total 5 packets.
- These packets are then sent one after the other.
Data Sent in One Packet-
Data sent in one packet
= Total data to be sent / Number of packets
= 1000 bytes / 5
= 200 bytes
Size Of One Packet-
Packet size
= 200 bytes of data + 100 bytes of header
= 300 bytes
Transmission Delay-
Transmission delay
= Packet size / Bandwidth
= 300 bytes / 1 MBps
= 300 x 10-6 sec
= 300 μsec
= 0.3 msec
Time Taken By First Packet-
Time taken by the first packet to reach from sender to receiver
= 3 x Transmission delay
= 3 x 0.3 msec
= 0.9 msec
Time Taken By Remaining Packets-
Time taken by the remaining packets to reach from sender to receiver
= Number of remaining packets x Transmission delay
= 4 x 0.3 msec
= 1.2 msec
Total Time Taken-
Total time taken to send the complete message from sender to receiver
= 0.9 msec + 1.2 msec
= 2.1 msec
Case-03: Sending Data in 10 packets-
In this case,
- The entire message is divided into total 10 packets.
- These packets are then sent one after the other.
Data Sent in One Packet-
Data sent in one packet
= Total data to be sent / Number of packets
= 1000 bytes / 10
= 100 bytes
Size Of One Packet-
Packet size
= 100 bytes of data + 100 bytes of header
= 200 bytes
Transmission Delay-
Transmission delay
= Packet size / Bandwidth
= 200 bytes / 1 MBps
= 200 x 10-6 sec
= 200 μsec
= 0.2 msec
Time Taken By First Packet-
Time taken by the first packet to reach from sender to receiver
= 3 x Transmission delay
= 3 x 0.2 msec
= 0.6 msec
Time Taken By Remaining Packets-
Time taken by the remaining packets to reach from sender to receiver
= Number of remaining packets x Transmission delay
= 9 x 0.2 msec
= 1.8 msec
Total Time Taken-
Total time taken to send the complete message from sender to receiver
= 0.6 msec + 1.8 msec
= 2.4 msec
Case-04: Sending Data in 20 Packets-
In this case,
- The entire message is divided into total 5 packets.
- These packets are then sent one after the other.
Data Sent in One Packet-
Data sent in one packet
= Total data to be sent / Number of packets
= 1000 bytes / 20
= 50 bytes
Size Of One Packet-
Packet size
= 50 bytes of data + 100 bytes of header
= 150 bytes
Transmission Delay-
Transmission delay
= Packet size / Bandwidth
= 150 bytes / 1 MBps
= 150 x 10-6 sec
= 150 μsec
= 0.15 msec
Time Taken By First Packet-
Time taken by the first packet to reach from sender to receiver
= 3 x Transmission delay
= 3 x 0.15 msec
= 0.45 msec
Time Taken By Remaining Packets-
Time taken by the remaining packets to reach from sender to receiver
= Number of remaining packets x Transmission delay
= 19 x 0.15 msec
= 2.85 msec
Total Time Taken-
Total time taken to send the complete message from sender to receiver
= 0.45 msec + 2.85 msec
= 3.3 msec
Observations-
- When data is sent in 1 packet, total time taken = 3.3 msec
- When data is sent in 5 packets, total time taken = 2.1 msec
- When data is sent in 10 packets, total time taken = 2.4 msec
- When data is sent in 20 packets, total time taken = 3.3 msec
Conclusion-
We conclude-
- Total time decreases when packet size is reduced but only up to a certain limit.
- If the packet size is reduced beyond a certain limit, then total time starts increasing.
From the given choices,
- Sending the message in 5 packets would be most efficient.
- In other words, packet size = 300 bytes would be the best choice.
Types of Packet Switching-
Packet switching may be carried out in the following 2 ways-
- Virtual Circuit Switching
- Datagram Switching
Virtual Circuit Switching-
Virtual circuit switching operates in the following three phases-
- Establishing a circuit
- Transferring the data
- Disconnecting the circuit
1. Establishing A Circuit-
In this phase,
- A logical connection is established between the two ends.
- It provides a dedicated path for data to travel from one to the other end.
- Resources are reserved at intermediate switches which are used during the transmission.
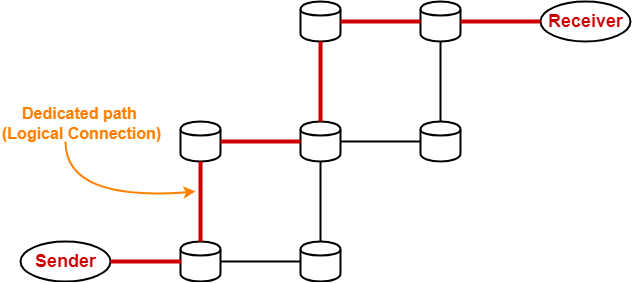
2. Transferring The Data-
After the connection is established,
- The entire data travels over the dedicated path from one end to the other end.
3. Disconnecting The Circuit-
After the data transfer is completed,
- The connection is disconnected.
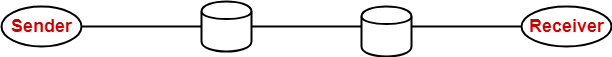
Datagram Switching-
In datagram switching,
- There exists no dedicated path for data to travel.
- The header of each packet contains the destination address.
- When any intermediate switch receives the packet, it examines its destination address.
- It then consults the routing table.
- Routing table finds the corresponding port through which the packet should be forwarded.
Virtual Circuit Switching Vs Datagram Switching-
The following table shows a comparison between virtual circuit switching and datagram switching-
| Virtual Circuit Switching | Datagram Switching |
| The first packet during its transmission-
1) Informs the intermediate switches that more packets are following. 2) Reserve resources (CPU, bandwidth and buffer) for the following packets at all the switches on the way. |
The first packet does not perform any such task during its transmission. |
| The packets are never discarded at intermediate switches and immediately forwarded since resources are reserved for them. | The packets may be discarded at intermediate switches if sufficient resources are not available to process the packets. |
| It is a connection oriented service since resources are reserved for the packets at intermediate switches. | It is a connection less service since no resources are reserved for the packets. |
| All the packets follow the same dedicated path. | All the packets take path independently. |
| Data appears in order at the destination since all the packets take the same dedicated path. | Data may appear out of order at the destination since the packets take path independently. |
| It is highly reliable since no packets are discarded. | It is not reliable since packets may be discarded. |
| It is costly. | It is cost effective. |
| Only first packet requires a global header which identifies the path from one end to other end.
All the following packets require a local header which identifies the path from hop to hop. |
All the packets require a global header which contains full information about the destination. |
| ATM (Asynchronous Transfer Mode) uses virtual circuit switching. | IP Networks use datagram switching. |
| Virtual circuit switching is normally implemented at data link layer. | Datagram switching is normally implemented at network layer. |
PRACTICE PROBLEM BASED ON PACKET SWITCHING TECHNIQUE-
Problem-
In a packet switching network, packets are routed from source to destination along a single path having two intermediate nodes. If the message size is 24 bytes and each packet contains a header of 3 bytes, then the optimum packet size is-
- 4 bytes
- 6 bytes
- 7 bytes
- 9 bytes
Solution-
Let bandwidth of the network = X Bps and 1 / X = a
Option-A: Packet Size = 4 Bytes
In this case,
- The entire message is divided into packets of size 4 bytes.
- These packets are then sent one after the other.
Data Sent in One Packet-
Data size
= Packet size – Header size
= 4 bytes – 3 bytes
= 1 byte
Thus, only 1 byte of data can be sent in each packet.
Number Of Packets-
Number of packets required
= Total data to be sent / Data contained in one packet
= 24 bytes / 1 byte
= 24 packets
Transmission Delay-
Transmission delay
= Packet size / Bandwidth
= 4 bytes / X Bps
= 4a sec
Time Taken By First Packet-
Time taken by the first packet to reach from sender to receiver
= 3 x Transmission delay
= 3 x 4a sec
= 12a sec
Time Taken By Remaining Packets-
Time taken by the remaining packets to reach from sender to receiver
= Number of remaining packets x Transmission delay
= 23 x 4a sec
= 92a sec
Total Time Taken-
Total time taken to send the complete message from sender to receiver
= 12a sec + 92a sec
= 104a sec
Option-B: Packet Size = 6 bytes
In this case,
- The entire message is divided into packets of size 6 bytes.
- These packets are then sent one after the other.
Data Sent in One Packet-
Data size
= Packet size – Header size
= 6 bytes – 3 bytes
= 3 bytes
Thus, only 3 bytes of data can be sent in each packet.
Number Of Packets-
Number of packets required
= Total data to be sent / Data contained in one packet
= 24 bytes / 3 bytes
= 8 packets
Transmission Delay-
Transmission delay
= Packet size / Bandwidth
= 6 bytes / X Bps
= 6a sec
Time Taken By First Packet-
Time taken by the first packet to reach from sender to receiver
= 3 x Transmission delay
= 3 x 6a sec
= 18a sec
Time Taken By Remaining Packets-
Time taken by the remaining packets to reach from sender to receiver
= Number of remaining packets x Transmission delay
= 7 x 6a sec
= 42a sec
Total Time Taken-
Total time taken to send the complete message from sender to receiver
= 18a sec + 42a sec
= 60a sec
Option-C: Packet Size = 7 bytes
In this case,
- The entire message is divided into packets of size 7 bytes.
- These packets are then sent one after the other.
Data Sent in One Packet-
Data size
= Packet size – Header size
= 7 bytes – 3 bytes
= 4 bytes
Thus, only 4 bytes of data can be sent in each packet.
Number Of Packets-
Number of packets required
= Total data to be sent / Data contained in one packet
= 24 bytes / 4 bytes
= 6 packets
Transmission Delay-
Transmission delay
= Packet size / Bandwidth
= 7 bytes / X Bps
= 7a sec
Time Taken By First Packet-
Time taken by the first packet to reach from sender to receiver
= 3 x Transmission delay
= 3 x 7a sec
= 21a sec
Time Taken By Remaining Packets-
Time taken by the remaining packets to reach from sender to receiver
= Number of remaining packets x Transmission delay
= 5 x 7a sec
= 35a sec
Total Time Taken-
Total time taken to send the complete message from sender to receiver
= 21a sec + 35a sec
= 56a sec
Option-D: Packet size = 9 Bytes
In this case,
- The entire message is divided into packets of size 9 bytes.
- These packets are then sent one after the other.
Data Sent in One Packet-
Data size
= Packet size – Header size
= 9 bytes – 3 bytes
= 6 bytes
Thus, only 6 bytes of data can be sent in each packet.
Number Of Packets-
Number of packets required
= Total data to be sent / Data contained in one packet
= 24 bytes / 6 bytes
= 4 packets
Transmission Delay-
Transmission delay
= Packet size / Bandwidth
= 9 bytes / X Bps
= 9a sec
Time Taken By First Packet-
Time taken by the first packet to reach from sender to receiver
= 3 x Transmission delay
= 3 x 9a sec
= 27a sec
Time Taken By Remaining Packets-
Time taken by the remaining packets to reach from sender to receiver
= Number of remaining packets x Transmission delay
= 3 x 9a sec
= 27a sec
Total Time Taken-
Total time taken to send the complete message from sender to receiver
= 27a sec + 27a sec
= 54a sec
Observations-
From here,
- Total time taken when packet size is 4 bytes = 104a sec
- Total time taken when packet size is 6 bytes = 60a sec
- Total time taken when packet size is 7 bytes = 56a sec
- Total time taken when packet size is 9 bytes = 54a sec
Result-
Time taken is minimum when packet size is 9 bytes.
Thus, Option (D) is correct.
To gain better understanding about Packet Switching,
Next Article- Circuit Switching Vs Packet Switching
Get more notes and other study material of Computer Networks.
Watch video lectures by visiting our YouTube channel LearnVidFun.